Theme: Single Sign-on (SSO)
Single sign-on (SSO) enables end-users to log in once, after which automatic access is provided to multiple applications and information sources in the organization’s network.
For example, a user logs in on his/her computer after which, behind the scenes, communication protocols can also be used to automatically log in to, for example, network facilities. The end-user does not have to log in every time, and the login screen is no longer shown.
The advantages of single sign-on are:
- Simplicity for the user: one authentication method for countless applications
- The user is more productive: less time spent on procedures, searches, etc.
- Provides the opportunity to tighten up the only remaining login procedure and make the digital network more secure.
SSO methods
There are various SSO techniques available. Currently, we offer 2 options with Comm’ant:
- Authentication based on the local/on-prem Active Directory of your Windows server environment
This method assumes that the server on which the Comm’ant application runs is included in the local network of the organization. In this case, Comm’ant only allows users that are actually logged into the local network. Based on the Windows network SID (unique identifier of the user) a match is made with the Comm’ant user base. - Authentication based on the Microsoft Azure Active Directory (Azure AD tenant)
This method authenticates the user against your organization’s Microsoft Azure Active Directory. Because this method is not tied to the local network, it can work perfectly with our cloud solution. The Comm’ant management system can be hosted within any cloud environment (Comm’ant’s, but also, for example, Azure’s), yet only be available to users who are matched against your Active Directory. This method has another advantage: you can more easily offer external users (temporary) access to the management system, without giving them access to your internal network. More on this later.
SSO and user synchronization
A Single Sign-on solution offers another very practical advantage: it can greatly simplify user management.
The Comm’ant system works with named users. After users identify themselves, they have access to information that is tailored to their Function. These users must of course be entered into the Comm’ant system.
But if you use one of the SSO solutions mentioned above, a process is set up to ensure that every night (or more often if you wish) there is a synchronization between the users in your Active Directory (on-prem or in the Azure cloud) and those in Comm’ant. New users are automatically added to Comm’ant. Users that no longer appear in your Active Directory are also no longer visible in Comm’ant (and of course no longer have access).
Often 1 or more Security Groups are created within your Active Directory specifically for Comm’ant. For example, one group for “All employees” and a group for “Guests / Externals”. This makes it easy for your IT organization to manage Comm’ant users.
After each synchronization, a specific synchronization report is sent to the designated administrator for confirmation/verification.
With the SSO Azure solution combined with Self-service Group management, you are even more flexible. Read more about Self-service Group management below.
Single Sign-on with Guest Users
Do you work with Single Sign-on and want to give guest users access to your Comm’ant environment? Then SSO via Azure AD with multiple Security Groups is an effective solution.
- Allow guests to log in via SSO with their own Microsoft account (or temporarily give your guests a Windows account from your company).
- Keep a good overview of who the relevant guest users are.
- Leave the management to the person directly responsible (functional or application manager).
The SSO configuration is initially set up for your own employees, those who have a Microsoft account with a login name in your Active Directory.
In the Active Directory, a security group is assigned, in which the selected users are included and this security group is linked to the Comm’ant environment.
If you want to grant external or guest users access to your Comm’ant system, you can create one or more additional Security Groups for that within your Azure AD and manage them via Self-service Group management. If a functional or application administrator is assigned the appropriate rights within the Azure management environment, he or she can easily add and remove external users to these groups via a web interface.
How does Self-service Group management work?
If you, as a functional or application administrator, have been assigned the appropriate permissions by your IT organization or Azure AD administrator, you can manage users through Microsoft Azure’s MyApps management environment.
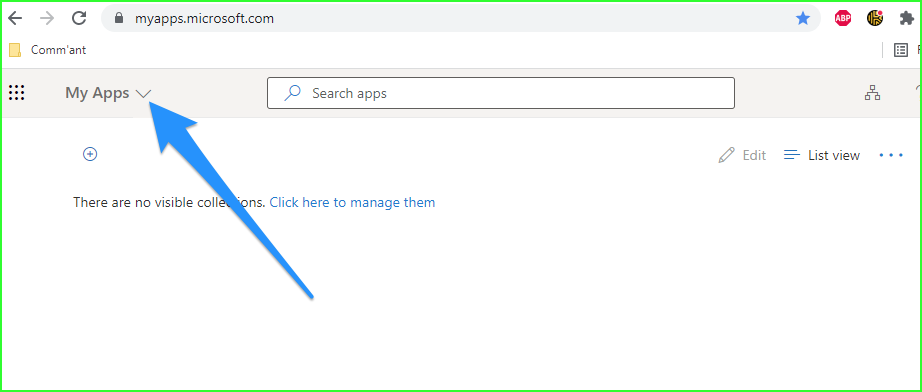
- Go to https://myapps.microsoft.com/
- And use the menu “My apps” to go to “My groups”
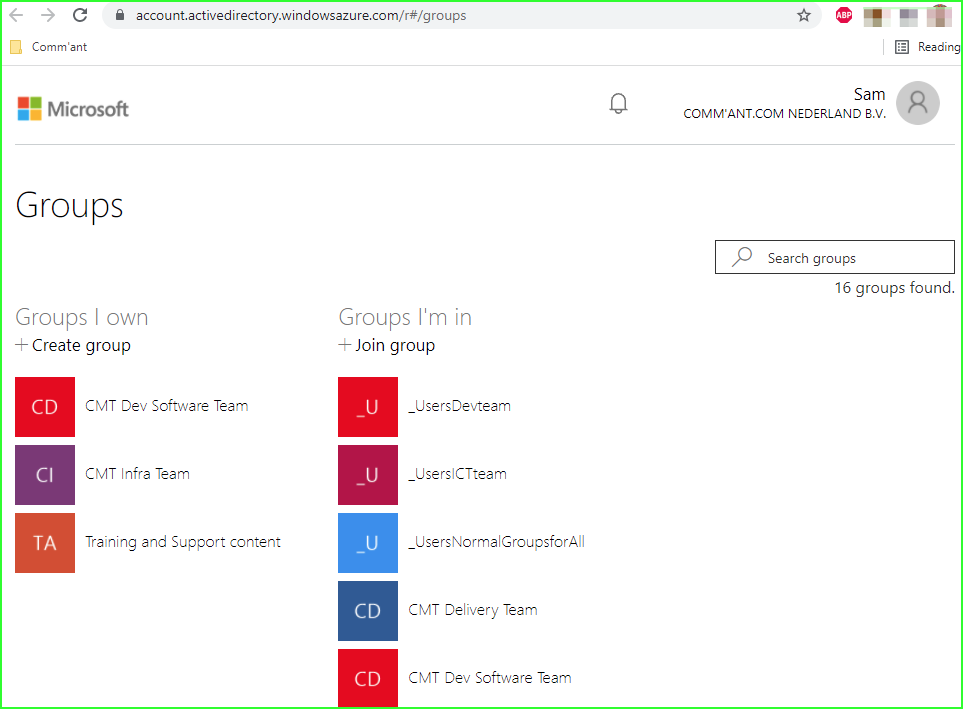
If all went well, your IT organization has already created a special group that you can manage. In this example, this is called “Comm’ant X external users”.
- Select this group
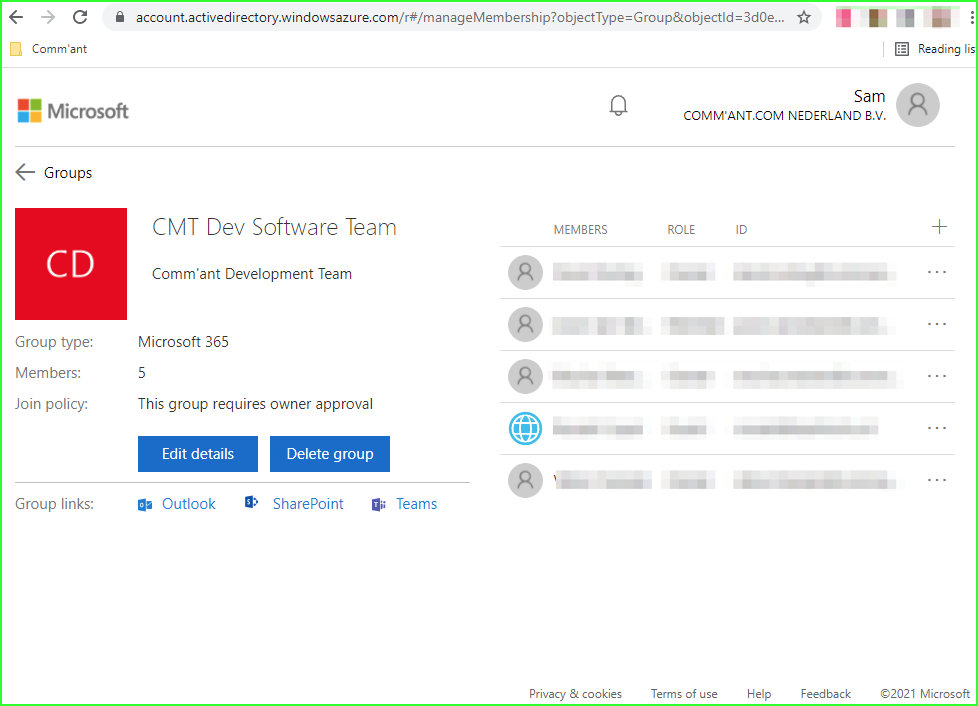
- You can add users via the +-sign on the right.
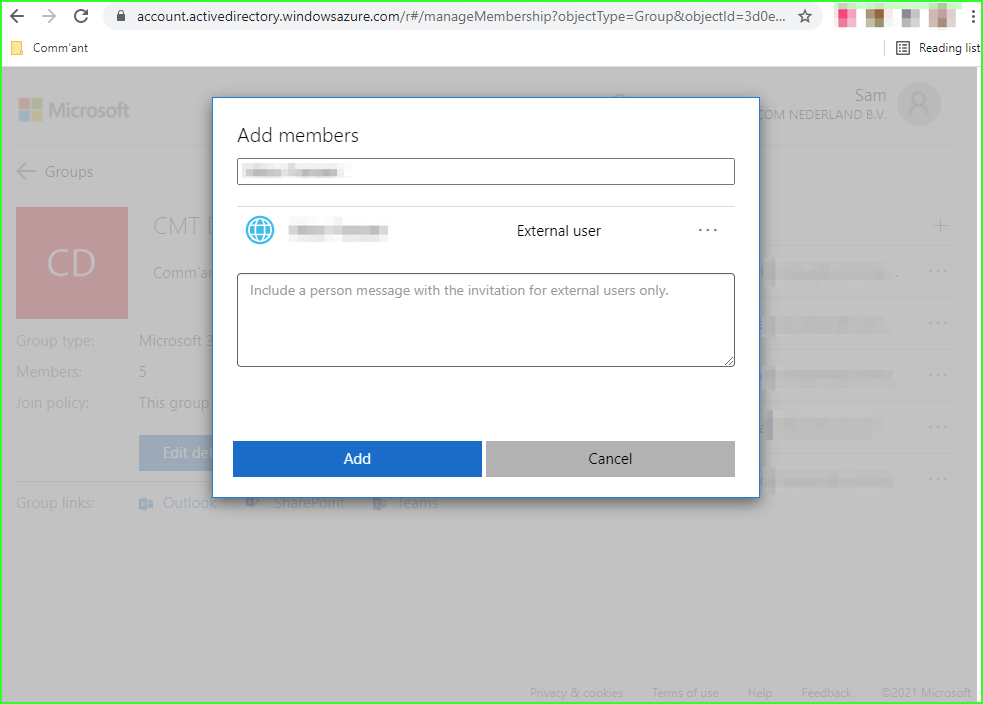
- You can add a user by entering his/her email address and clicking “Add”.
- The prerequisite is that the specified email address has a Microsoft account associated with it. If this is not the case, the user will not be accepted.
- If the external user does not have a Microsoft account he/she can easily create one here: https://account.microsoft.com/
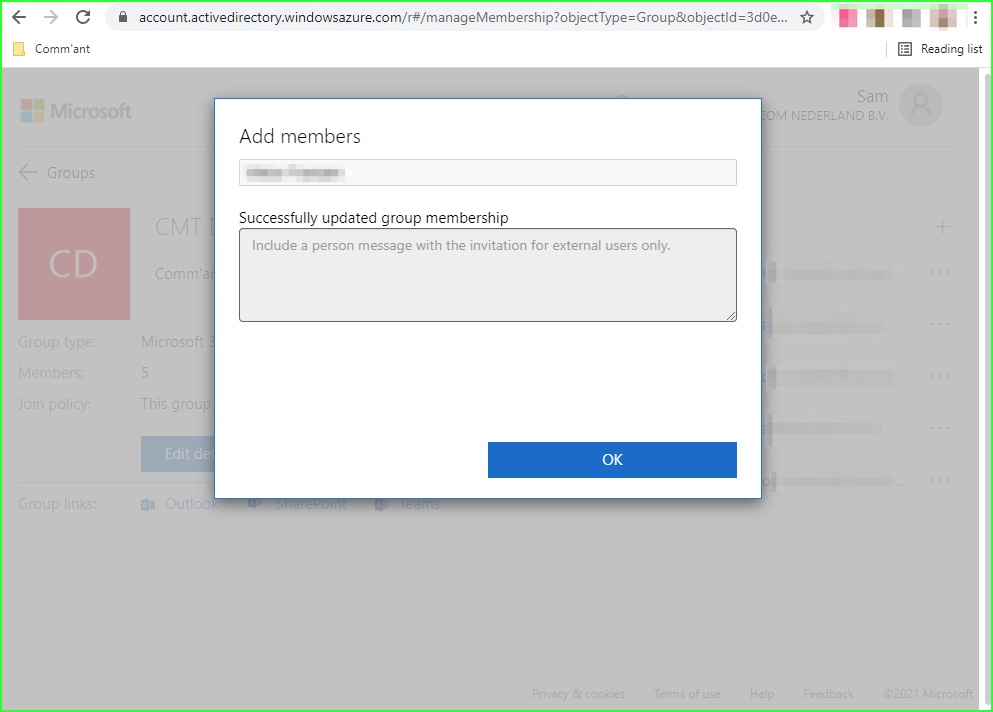
If the new user is accepted a confirmation screen appears:
- Click “OK” to continue.
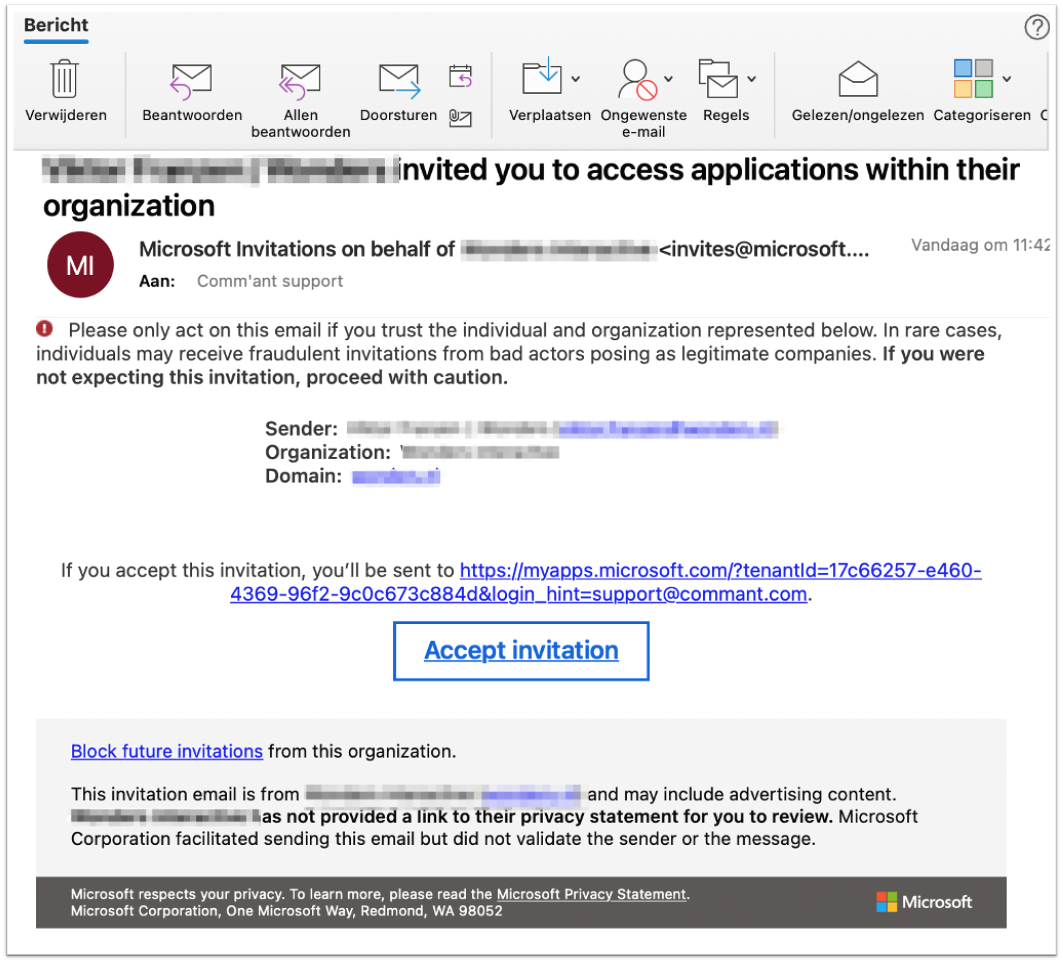
- The user in question will receive an invitation by email that he/she will have to accept in order to gain access to the Comm’ant application.
The confirmation email will look something like this:
Important: depending on the settings and the moment of adding the user to the Security Group, it can take up to 24 hours before the user actually has access to your Comm’ant management system, after he/she has accepted the invitation. After all, the synchronization process still has to take place. This usually happens at night.
The next time the new user goes to the address of your Comm’ant management system he/she will be confronted with the Microsoft login screen of your organization. Read more about logging in with SSO here.